In a “Socks Rocks! The Good, The Bad and The Ugly” post, I wrote about configuring OpenVPN, TOR and Proxifier in order to hide the real IP and use web sites such as Google which do not allow lots of services for TOR exit nodes.
Literally, the ugly is removed from the previous post and openvpn directly connects to socks.
The Problem
When using the Internet, one may want to use TOR for surfing the net. The problem arise here where some sites block access to the site from the TOR network, more specifically they block the IP addresses of the EXIT Nodes, sites such as Google or CloudFlare or (optionally) BlockChain Wallet.
Previous Solution
Previously, I published a post about how to configure proxychains to tunnel the traffic between client (PC) and VPN Server (openvpn). Proxychains is a tunneling software for flowing the traffic through proxy servers; in this case TOR socks address where the TOR runs. Usually this address is 127.0.0.1:9050 or 127.0.0.1:9150.
The Problem with ProxyChains
I have faced connection problems where if for some times you do not use the Internet, proxychains will disconnect the traffic between PC and openvpn server. For solving this problem I made an infinitive ping request, so the connection is alive all the time.
Better Socks Rocks
A better solution I’ve found recently is the built-in support of proxifying connection in openvpn client. But you should use the default client, not the limited ones that published by others.
The following pictures shows the Settings in openvpn and the configuration for using TOR.


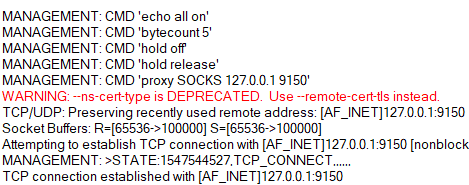
Result
If you want to use TOR but do not want to get restricted connection, you can connect to openvpn server through TOR Socks5 proxy. Now your real IP is hidden from openvpn server (and the sites you visit them) but the exit node is not TOR but it is OpenVPN.
It is reasonable to got an increase in reply time of packets. As an example I get 300-400 ms time in pinging 8.8.8.8



آقا یک سوال
این openVPN یک سرور هم میخواد
Tor که رایگانه و openSource
اما OpenVPN خب یک سرور میخواد
بله. صحبتتان صحیح است. یا باید خودتان راه اندازی کنید یا باید از یکجایی تهیه کنید.
البته احتمال دارد وی پی انهای دیگری نیز باشد که SOCKs را پشتیبانی کنند.
مطلب خوب و کاملی بود.فقط توی این بررسی wireguard را نیاوردید.
با سلام. خودم نیز همین دیروز آشنا شدم. سرور Algo نصب کردم و با WireGuard متصل شدم. فعلا در حال بررسی هستم. ممنون از توجهتان.