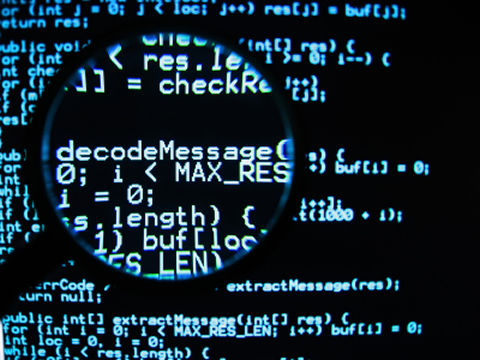
ASIS2014: NUMDROID WRITE-UP
I’ve playing with Android CTF questions recently and found this jewelry box. One of the questions was about a numeric one way hash question named NUMDROID. The question was presented in ASIS2014 and here, I write the write-up!